Adversarial Vulnerability Intelligence
The authority on real-world exploitability
From 1,500+ sources to one intelligent view. Securin's AI-powered Data Fabric unifies scanners, EDR, cloud, CMDB, SIEM and AI workloads into one living map of your environment.
Where data becomes adversarial intelligence
Most platforms show you vulnerabilities.
Securin shows you intent — what attackers are targeting, exploiting, and weaponizing right now.
By combining AI-driven analytics, expert intelligence, and the industry's deepest exploit dataset, Securin transforms vulnerability data into predictive, adversarial insight you can act on immediately.
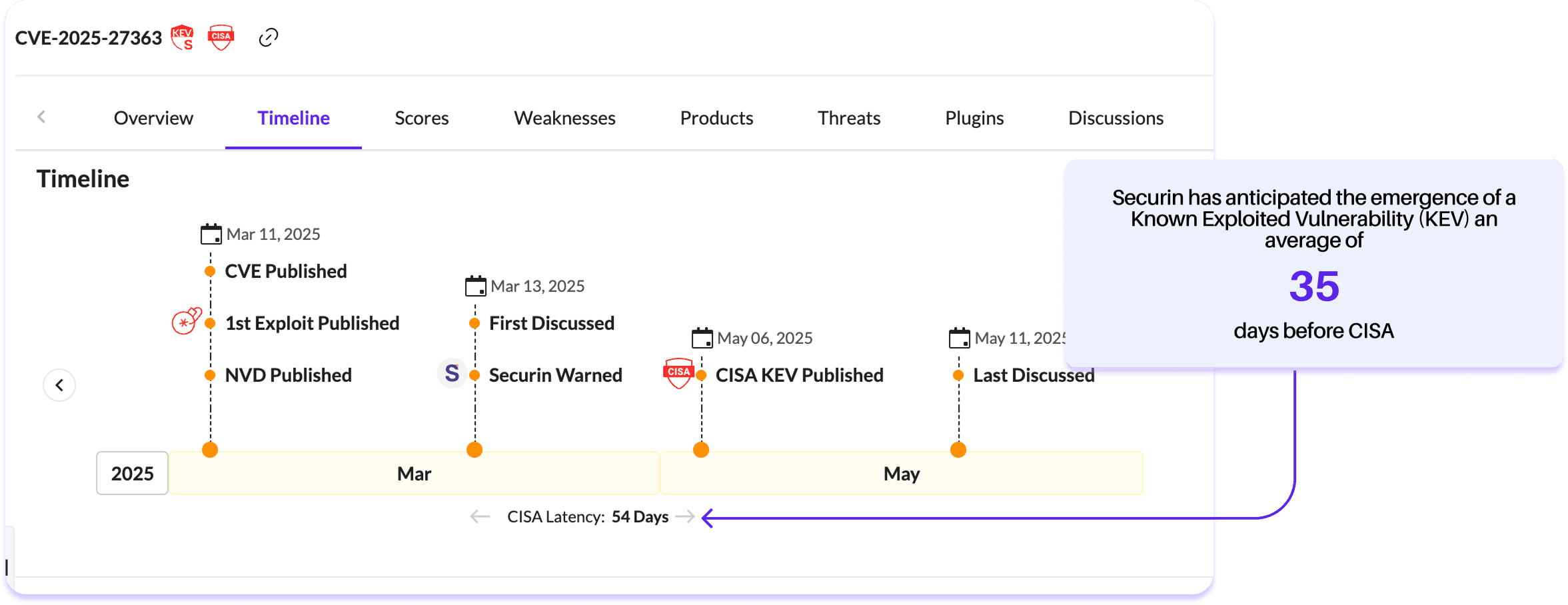
Faster KEV detection
than CISA's public listings
More KEVs identified & tracked
through proprietary intelligence fusion
Curated intelligence sources
continuously monitored across dark web, OSINT, and commercial feeds
Resolution rate
for ransomware-related vulnerabilities.
Securin shows you intent — what attackers are targeting, exploiting, and weaponizing right now.
Key Capabilities
A ground-breaking, AI-first approach to adversarial exposure management. Our unified platform gives an adversary's view of your entire environment, so you can fix what matters most – and prove it worked.

Exploit prediction
Predict which vulnerabilities will be weaponized before proof-of-concept code emerges.
- • Pre-PoC indicators
- • Exploit latency analysis
- • Early adversary chatter detection

Threat actor tracking
Correlate CVEs with ransomware groups, APT campaigns, and exploit kit integrations.
- • APT campaign mapping
- • Ransomware targeting patterns
- • Exploit chain intelligence

Real-time intelligence
Stay current with continuously updated signals from 1,500+ curated sources.
- • Live threat feeds
- • OSINT, social media, and underground forum monitoring
- • Global disclosure tracking

Contextual enrichment
Layer business context, asset criticality, and attack path analysis for actionable prioritization.
- • Asset-based risk scoring
- • Business impact assessment
- • Environmental correlation
Securin's data fabric normalizes, enriches, and correlates every signal — transforming raw data into unified, adversarial intelligence.
Intelligence Lifecycle
Continuous feedback loop powered by adversarial intelligence





Proof at every step. One engine, zero blind spots.
One intelligence source. One adversarial perspective.
Securin's Vulnerability Intelligence Engine powers the full AEVOps ecosystem — from discovery to validation — and stands alone as the authoritative source of truth for real-world exploitability.