Know what's next.
Not just what's out there.
One source of truth. One prioritized list. One unified view of your risk.
One platform for adversarial intelligence, continuous validation and AI-driven clarity. Turn exposure data into contextual unified exposure management, powered by a purpose-built data fabric that adapts to your unique environment.
Predict exploits. Prioritize what adversaries are targeting. Validate your defenses.
Connect every exposure to real-world risk. Make insight actionable.
Built from 1,500+ curated intelligence sources and 1.58 million library components, Securin's Data Fabric unifies hundreds of siloed security integrations — spanning scanners, EDR, cloud, CMDB, and AI workloads — into one continuously updated, AI-powered operational view of your environment.
AI-ready by design, enriched across three dimensions

Susceptibility
Scanner and NVD data to establish exposure baselines.

Temporal
Time and decay dynamics to track exploit evolution and weaponization.

Environmental
Business-layer and CMDB intelligence for contextual prioritization.
Operationally integrated for speed and proof
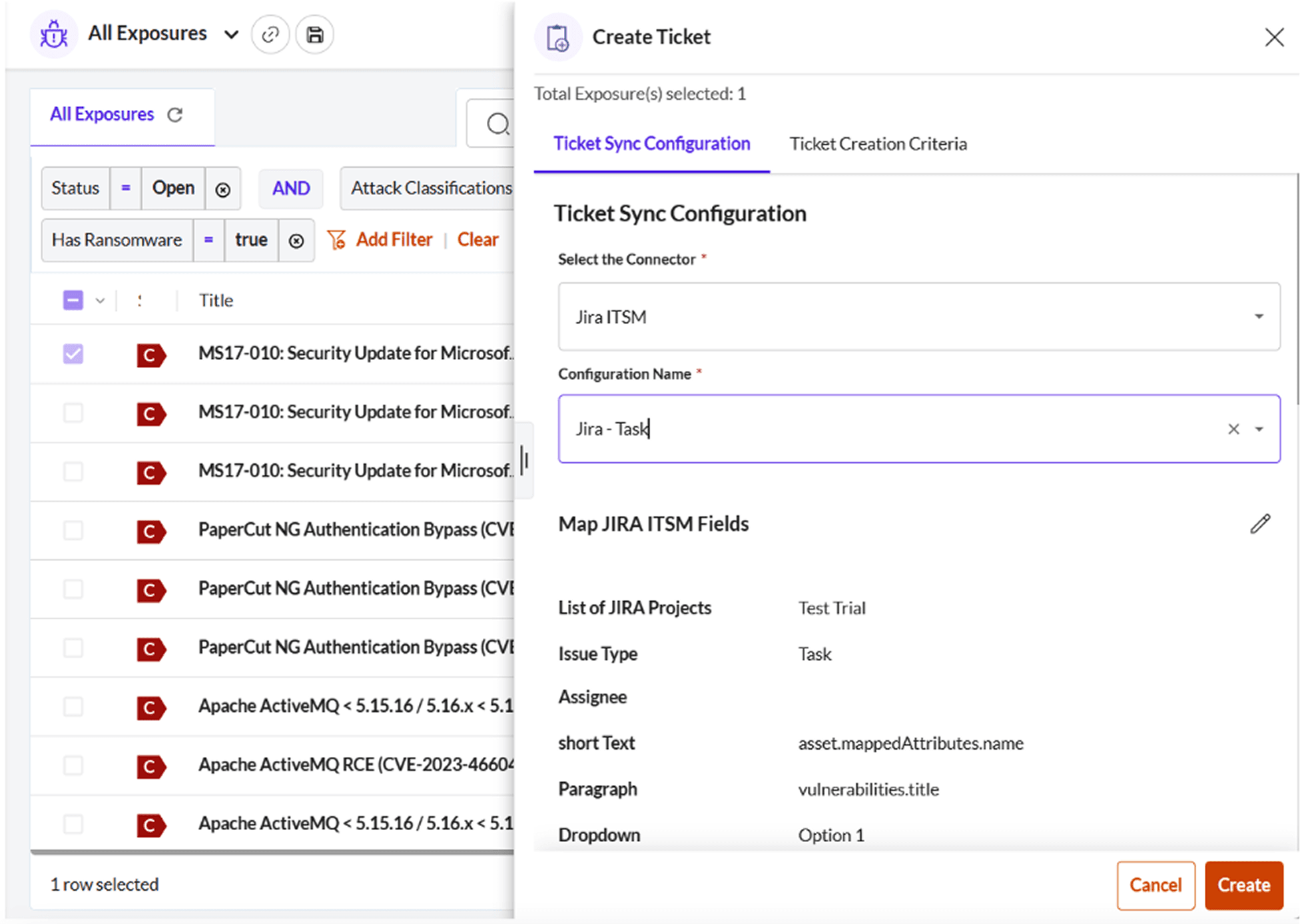
Validation where work happens
Writes directly to Jira and ServiceNow for IT and developer workflows.
Ready for agents and automation
Connects seamlessly with MCP and agent-based integrations.
AI-ready by design
Prepares data for AI tools and pipelines, ready for automated analysis and validation.
Any exposure. Any system. One living source of truth.
Integrates with your environment










Securin Data Fabric
Connect every exposure to real-world risk. Make insight actionable.
Don't just track exposures - forecast which ones will be weaponized next, focus on what adversaries are actually after, and validate defensibility. Built on Securin Core and powered by AEVOps, Unified Exposure Management turns fragmented data into predictive, operational foresight — all through one purpose-built Data Fabric. It's the consolidation engine that de-duplicates and correlates all your data into a single language of risk, without the dashboard hopping.
From disclosure to weaponization
Correlate CVEs with pre-PoC signals, exploit code, and in-the-wild activity to predict which vulnerabilities adversaries will target next.
- Pre-PoC indicators and campaign chatter
- Exploit availability and active use
- Time-to-weaponization tracking
Root causes, not repeats
Move beyond individual CVEs by mapping recurring weaknesses to their underlying causes across applications and teams.
- Top software errors and patterns
- OWASP Top 10 alignment
- Structural risk, not one-off findings
When drift becomes risk
Not every misconfiguration matters. The Data Fabric connects configuration issues to reachability, access paths, and real attacker behavior.
- Exposure + access path correlation
- Prioritized by real exploit potential
- Noise reduced through context
Supply chain risk, in context
Understand which vulnerable libraries are actually reachable and exploitable in your environment — not just listed in an SBOM.
- Dependency reachability
- Blast radius across services
- Validation after upgrades and fixes
Normalized risk for agents
Expose correlated, structured risk signals that MCP and agent-based systems can reason over and act on automatically.
- Unified risk language
- Machine-consumable context
- Supports autonomous workflows
Exposure management for AI systems
Extend the Data Fabric to models, agents, APIs, and inference paths — where traditional exposure management stops.
- AI-specific attack surfaces
- Correlated with real-world threats
- Defensibility validated continuously
Predict weaponization
Pre-PoC indicators, campaign chatter.
Confirm exploitation
PoC code, in-the-wild use, kits, MITRE ATT&CK, cyber kill chain.
Exploit latency
Time from CVE discloser to first observed exploit.
Root cause
Top software errors, OWASP Top 10.
Impact you can see
Measurable results proven at scale. Operational proof of security effectiveness - not just tickets closed.
A continuously learning, AI-powered view of your environment — where insight, action, and evidence all flow from one purpose-built Data Fabric.
One fabric. One flow. One AEVOps cycle.
Securin's unified security data fabric keeps every phase connected —
Discover → Prioritize → Mitigate → Validate.
Stop chasing alerts. Start preventing attacks.