Threats now move faster than traditional intelligence.
KEVs weaponize in hours. Exploit chains form before teams see the first signal.
Adversarial Intelligence. Weaponization Awareness. AI-powered context for real-world threats.
Clear priorities, powered by AI and deeper data.
KEV catalog larger than CISA's
Zero days - discovered by our researchers
Patents registered
AI/ML models and 1,500+ curated sources
Get the intelligence right and every AEVOps decision becomes sharper, faster and adversary-aligned.
KEVs weaponize in hours. Exploit chains form before teams see the first signal.
— ATT&CK, threat blogs, social sources, dark web chatter — while attackers move with precision.
by unifying adversarial data, early weaponization signals, AI-driven analysis, and Deep/Dark Web insight into one authoritative source built for operational exposure reduction.
The adversarial intelligence engine for AEVOps
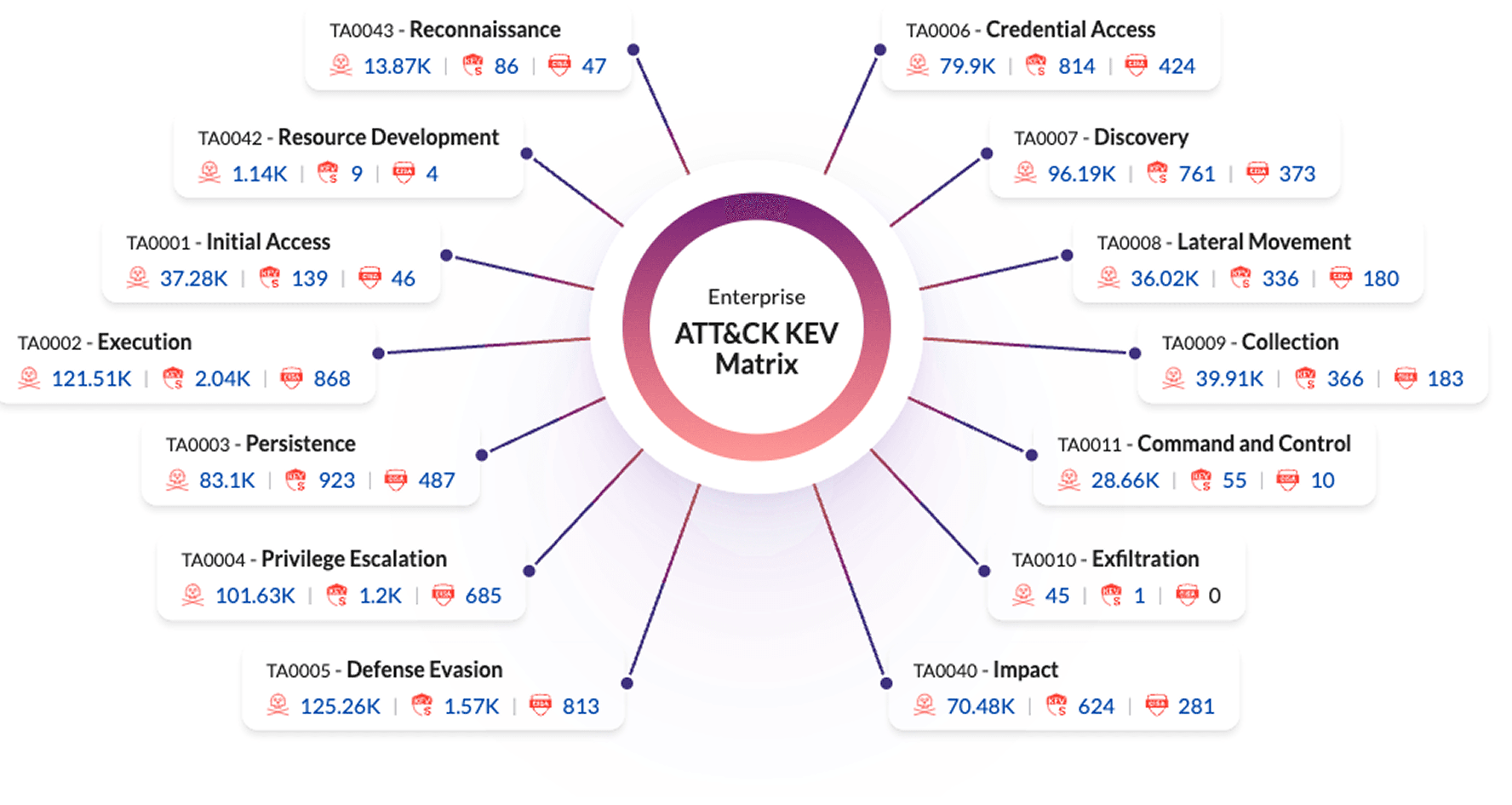
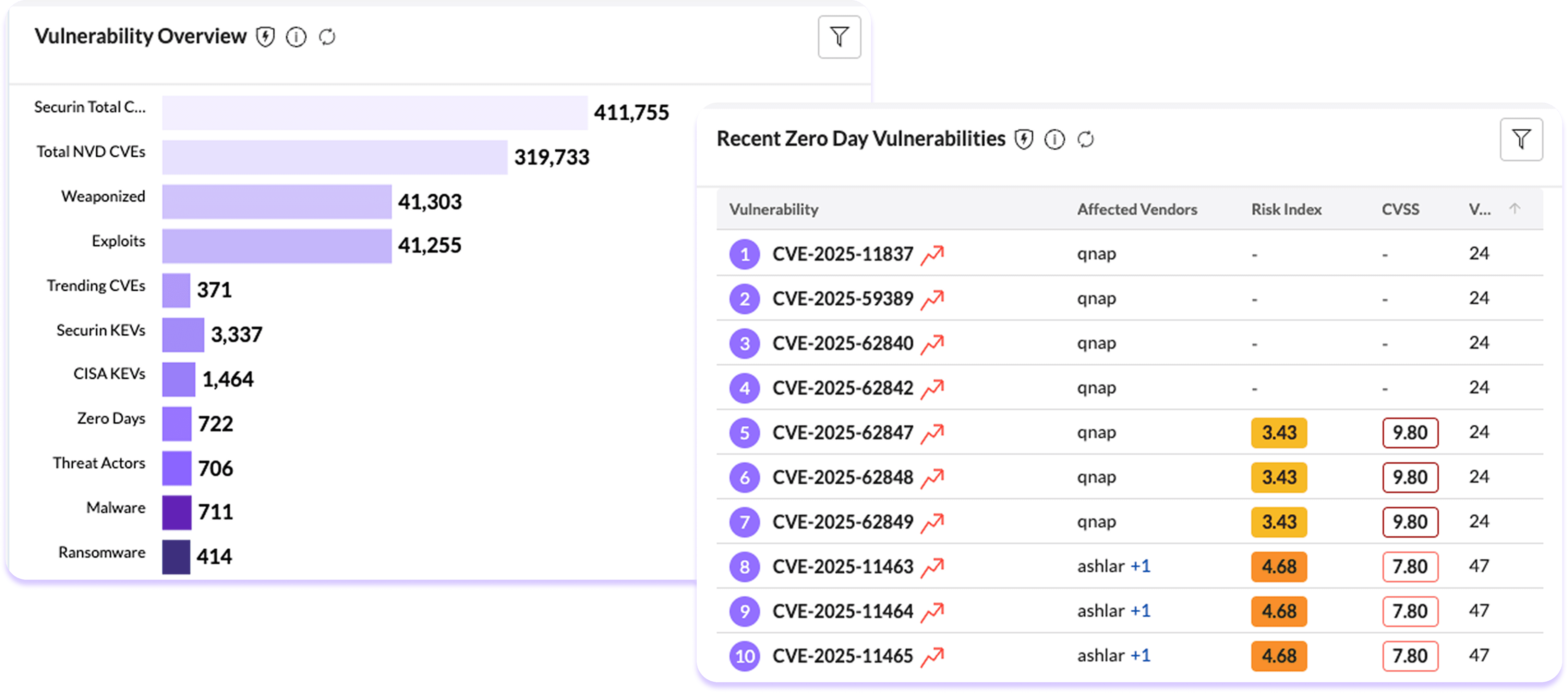
Securin Core mines 1500+ sources, fuses research from 100+ threat analysts, and maps the full CWE → CVE → KEV weaponization lifecycle with operational signal. It delivers the intelligence required to prioritize what matters — early, accurately, and in context. Securin Core maps every vulnerability into the MITRE ATT&CK matrix, revealing tactics, techniques, and real attacker behavior. Where CISA flags a slice of the threat landscape, Securin Core overlays a fuller spectrum:
More KEVs across more tactics
Earlier signals of weaponization
Deeper adversarial mapping for prioritization
One feed. All intelligence. Zero blind spots.
Track the evolution from weakness → vulnerability → exploit → active use in the wild. Prioritize before the peak — not after the breach.
Securin Core identifies ~2× more KEVs ~35 days earlier than CISA. Speed becomes foresight. Foresight becomes prevention.
Immediate visibility into campaigns, threat groups, ransomware families, and their exploit chains. Know who is using what, how, and against whom.
40× more credential, compromise, and adversarial chatter signals than OSINT alone. Your early-warning system — operationalized.
Turn subtle signals — odd IPs, hashes, anomalous traffic — into actionable context. Instant enrichment. Accelerated analyst workflow.
Audit open-source packages, OS components, MCP servers, and GenAI workloads. Surface risks no scanner touches — including package-level exposures and AI model weaknesses. Enhanced with Securin's AI Nutrition intelligence — turning AI models and components into readable, risk-ranked profiles.
The intelligence backbone of the operating model AEVOps runs on four motions — Discover → Prioritize → Remediate → Validate. Securin Core powers all four:
Identify emerging threats, weak signals, and adversarial pressure across the full exposure surface.
Rank vulnerabilities using exploitability, weaponization, threat actor activity, and ATT&CK alignment.
Guide teams toward the fixes that collapse real attacker paths — not the long tail of theoretical risk.
Confirm risk reduction through adversary-aware signal, not assumptions.
Without Securin Core, exposure handling is reactive. With Securin Core, every decision becomes adversary-aware and evidence-led.
Real impact — measurable, predictable, defensible.
Align security decisions to real adversarial pressure
Reduce risk before exploitation instead of after
Shrink analyst workload with one authoritative feed
Eliminate blind spots from missing plugins + fragmented intel
Move from information consumption to operational action
Prove security decisions with defensible, adversary-backed evidence
Securin Core gives teams clarity AEVOps turns clarity into outcomes.