Unknown assets appear outside IT control
Securin Sentry
Every external exposure. Ranked by exploitability.
The attack surface is expanding faster than teams can keep up.
Cloud | SaaS | Shadow IT | AI estates | Supply chain | Credential leaks | Posture drift Because external risk isn't everything you can see — it's everything attackers can reach.
KEVs weaponize fast — often within hours
Expired certs + open ports become instant access vectors
Prioritization is noisy, fragmented, operationally slow
3rd-party exposure is opaque
Risk posture is visible to attackers before it's visible internally
Enumeration isn't enough anymore. Security needs adversarial signal.
Introducing Securin Sentry
The outside-in intelligence engine for AEVOps
Securin Sentry scans, crawls and analyzes your entire external footprint - including dark web breach activity and posture drift - and turns it into one adversarially- prioritized exposure list.
An outside-in, adversarial view of your organization.
Go beyond vulnerabilities in the attack surface to find exposures internal scanners miss.
-
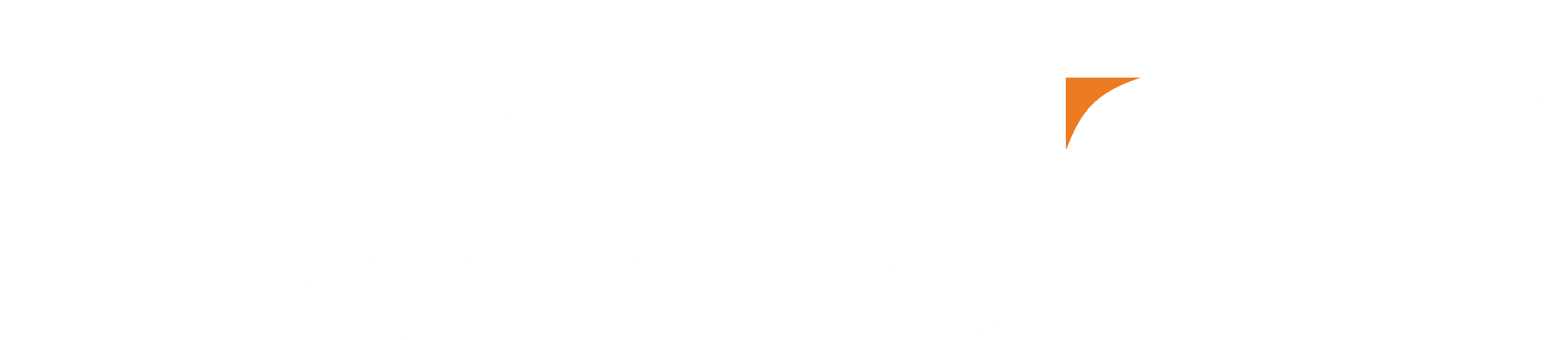
20–30% more unknown assets found - no blind perimeter.
-
Shadow IT, cloud sprawl, forgotten hosts - surfaced automatically.
-
No agent, no silos, no guessing — complete external enumeration across domains, clouds and workspaces.
-
Unknown assets become known. Known assets become manageable. Manageable assets become low risk.
Reveal what you don't know you own
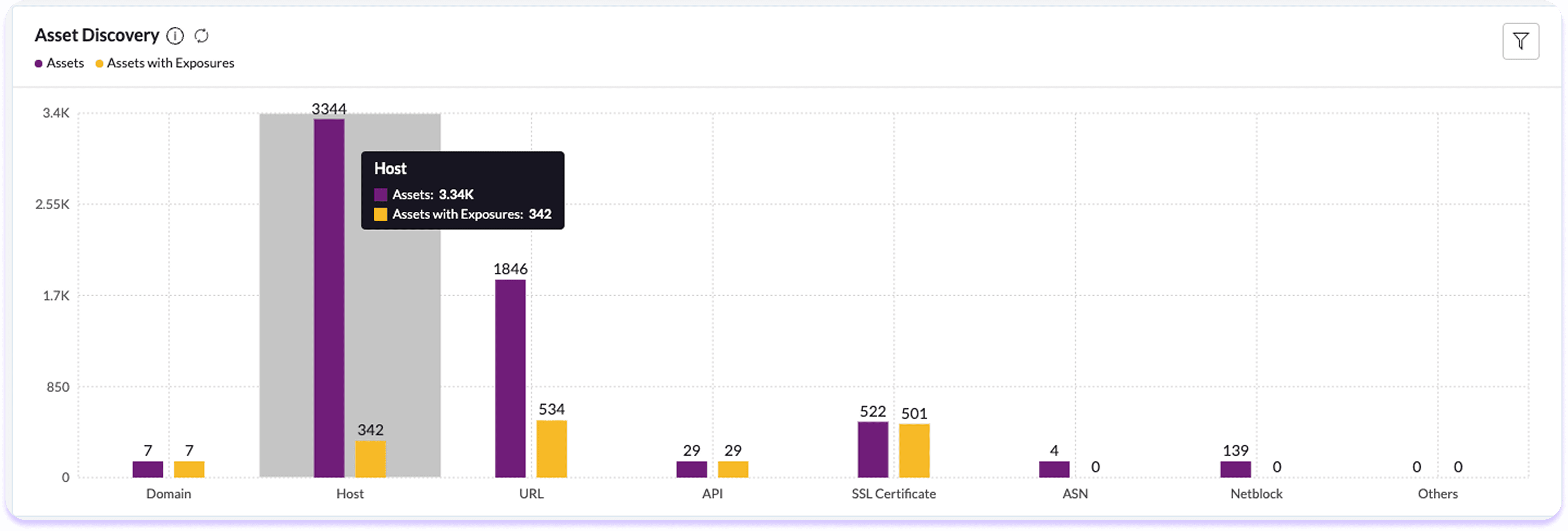
Shadow IT, cloud sprawl, and forgotten hosts – uncovered before attackers find them. Attackers don't just probe what you think is your perimeter. They probe everything tied to your IP space, cloud accounts and historical assets — including infrastructure your teams no longer track.
-
Misused IP blocks repointed to cloud experiments
-
Legacy services exposed long after teams believed them retired
-
Orphaned systems hosted in unexpected regions
-
Vendor-created infrastructure running on your certificates
Unknown assets become known. Known assets become manageable. Manageable assets become low risk.
Visibility becomes action. Action becomes advantage.
Average reduction in remediation timeframes
For CISA KEVs in 3-6 months
More KEVs Detected than CISA, up to 35 days faster
We surface vulnerabilities others are unaware of
Reduction in Priority List Size
within 3–6 months of deployment
How Securin Sentry Fits AEVOps
AEVOps = Discover → Prioritize → Remediate → Validate
AEVOps starts outside the firewall — this is Phase One.
Discover
Full outside-in visibility — plus Dark Web compromise signals
Prioritze
Exposure ordered by exploitability + business impact
Remediate
Feeds Triage and IT workflows with clean, ordered exposure data
Validate
Confirms posture hardening and external threat reduction
Securin Sentry exposes. Securin Triage executes. Securin Core powers both.
This is how AEVOps scales.