The Securin Platform
Unified. Continuous. Adversarially aware.
One platform for adversarial intelligence, continuous validation and AI-driven clarity. Break the silos. Eliminate the noise. Secure everything — from infrastructure to AI workloads.
CISA KEVs 35 days faster
Detects real-world exploits sooner
reduction in findings (3–6 mo)
Noise down, clarity up
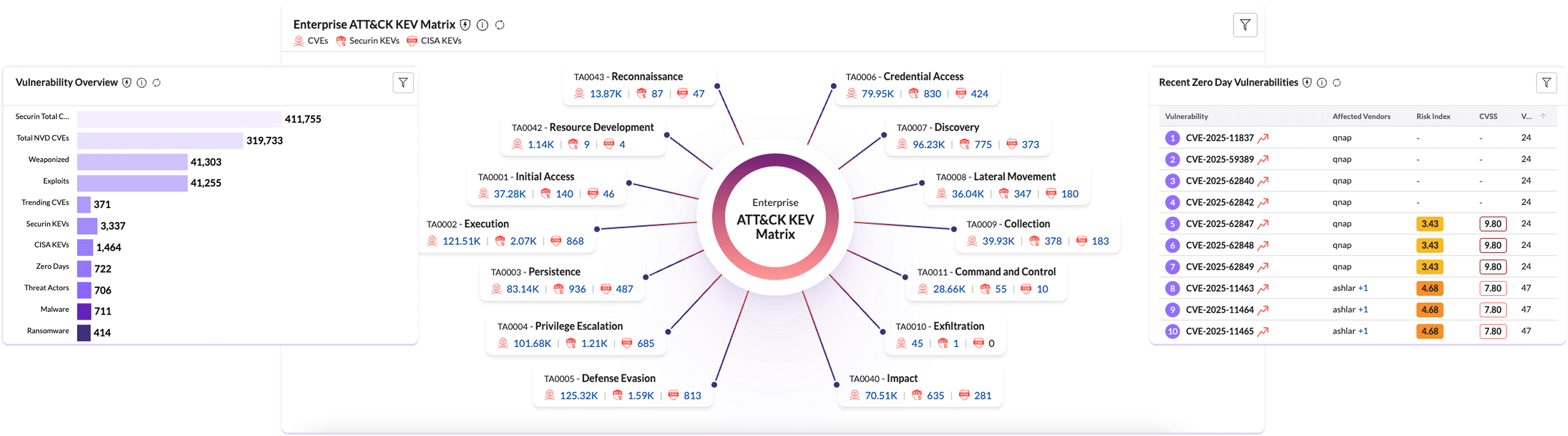
From fragmented data to Unified Adversarial Intelligence
One SaaS platform that ingests, correlates, and operationalizes risk data — eliminating silos and manual effort. Turn exposure intelligence into continuous defense.

Unified intelligence
Connects assets, exposures, and ownership across every tool and environment.

Adaptive data fabric
Normalizes data from any source into one living, real-time view.

AEVOps Foundation
Drives continuous validation, adversarial simulation, and risk-based prioritization.

Operational clarity
Transforms fragmented data into a single operational map for proactive defense.
One SaaS platform that ingests, correlates, and operationalizes risk data — eliminating silos and manual effort. Turn exposure intelligence into continuous defense.
Connected to everything that secures you
The platform connects directly with your SIEM, SOAR, ITSM, and vulnerability management tools to turn data into action.
SOAR and ITSM
VM and ASM Tools
AI and Cloud Workloads
Every signal. Every system. Consolidated and correlated through one continuously updated data fabric that adapts to your environment.
End-to-End Exposure Management:
Discover. Validate. Prove. Repeat.
Every capability operates through the same AI-powered fabric — one continuous security motion.
Securin Sentry
Continuous discovery and external attack-surface mapping.
Securin Core
AI-driven vulnerability intelligence from 1,000+ sources.
Securin Triage
Risk-based prioritization and ownership routing.
Securin Validate
Automated adversarial testing and proof of resilience.
Remediate
Executive-level reporting and verified closure.
Proof at every step. One Platform, zero silos. Built for AEVOps: Continuous, Contextual, Credible.
You See
- Weaponized CVEs in real time
- Reachable, high-value assets
- Fixes that cut breach risk
You Act
- No-code integrations with ITSM, SOAR, VM
- Intelligent routing & tracking
- Continuous AI-driven validation
Outcome
- Noise drops. MTTR shrinks. Clarity replaces chaos.
- You know what to fix first — and can prove it worked.
Securin Sentry exposes. Securin Triage executes. Securin Core powers both.
This is how AEVOps scales.